Techno Security & Digital Forensics Conference - MBSC - June 6-9, 2021

Over the past week, I was able to attend Techno Security and Digital Forensics Conference!
Achievement unlocked #TechnoSecurityMB #dfir pic.twitter.com/Nr8DFbqRkJ
— Jesse Spangenberger (@AzuleOnyx) June 6, 2021
You can find and follow the conference information on twitter with the hashtag #technosecuritymb
If you don't know what Techno Security is about, then from their site:
The Techno Security & Digital Forensics Conference brand has grown into one of the most important resources for corporate network security professionals, federal, state and local law enforcement digital forensic specialists, and cybersecurity industry leaders from around the world. The purpose is to raise international awareness of developments, teaching, training, responsibilities, and ethics in the field of IT security and digital forensics.
https://www.technosecurity.us/
The hotel was in a great place, as seen here from Noel Adams (link):
I did not stay at the hotel because I registered late, so I was down the road near the beach.
There was expresso in the vendor area provided by Belkasoft:
Do we smell a flavor of morning coffee? Come grab your espresso with optional creamer to the Belkasoft booth! And good morning!#DFIR #TechnoSecurityMB pic.twitter.com/AezBtgDtC7
— Belkasoft (@Belkasoft) June 7, 2021
There were many, many talks as well. I will highlight some of them which I attended. Since, I am bad with images, I'll link to some tweets as well.
Using Wi-Fi to Develop Case Leads and Improve Intelligence
Speaker: David Schwindt, Latent Wireless
1st talk today for me. Using wifi to develop case leads and improve intel. #technosecuritymb @technosecurity #dfir pic.twitter.com/L78yeRGgDf
— Noel Adams (@Noeladams) June 6, 2021
David Schwindt used two tools -- Kismet and channelhop -- in addition to Wireshark's tshark commandline tool for a demo on how to generate a list of devices and location them. You will need a WiFi adapter that supports monitor mode. You can check out Null-Byte's post "Buy the Best Wireless Newtork for Wi-Fi Hacking in 2019" for examples.
He also talked about documenting the GPS location for these devices. I cannot remember which GPS antenna he was using, but you can grab the GlobalSat BU-353-S4 on Amazon for around $30.
Forensics Analysis of Data Stored in SQLite
Speaker: Lynita Hinsch, Magnet Forensics
Forensics Analysis of Data Stored in SQLite databases. By Lynita Hinsch with @MagnetForensics Awesome job! Great info. pic.twitter.com/dQE4lfz3Yk
— Noel Adams (@Noeladams) June 6, 2021
Lynita's talk on SQLite had some great information and shared the book SQLite Forensics by Paul Sanderson. She went into how SQLite databases work and each of the different sections even pasted normal table and rows that most people know. Also, there was information on "deleted" data in the database which might not actually be deleted. Due to technical issues, she was unable to show the demos. You can get a feel for SQL DBs from DB Browser Tutorial for Beginners (YouTube).
Information Security in K-12 Education
Speaker: Noel Adams, Greenville County Schools
Haven't presented in years so today is my big day @technosecurity @gcschools
— Noel Adams (@Noeladams) June 6, 2021
Information Security in K12 #technosecuritymb https://t.co/l0QLwRLPSV pic.twitter.com/8MyaHDg0Jb
Noel showed how Greenville County Schools in South Carolina became ISO 27001:2013 certified. According to the timeline shown by Noel, this was over 12 years. I did ask if it could be compressed and it is probably possible to be certified in about 6 years. One participate at the conference did state you can pay upwards of $150,000 USD to have someone come in and help setup everything for you.
Why does the certification matter? It proves an organization has mature security program. It is the same reason why companies want security professionals to have certifications. There are ALOT of certifications (check Paul Jerimy's Security Certification Roadmap) unlike company security program certifications. As noted by Noel, NIST has great information and standards but is not a true certifications; Greenville County wanted to have an actual certification and ISO 27001:2013 fit the bill.
Taking Chromebook Analysis to New Heights
Speaker: Jessica L. Hyde, Magnet Forensics
Jessica has been researching Chromebooks since 2018. In 2019, she attended an event called Brews and Bytes for VTO Labs (YouTube). The event was to examine Chromebooks to see the amount of data you can retrieve off of them.
The event gained insight into the Chromebook's data including directly extracting data from the chips (chip-off). Today, Daniel Dickerson created a method to extract information from Chromebooks which you can read on DFRWS: Chromebook Forensic Acquisition. His method requires 3 USB drives but works to recovery data. Magnet Forensics worked with Daniel to create their MAGNET Chromebook Acquisition Assistant which uses a single drive but generally uses Daniel's method under the hood.
Media Analysis of Fake News and Intelligence
Speakers: Chet Hosmer, University of Arizona, and Mike Raggo, SilentSignals
Disinformation campaigns have really exploded during the last political cycle in the United States. Chet and Mike take a deep dive into the campaigns and demo a tool they use to detect fake images in online media.
These campaigns happen in a various of ways from Brand Impersonation, Keyword Squatting Malware, Shaming individuals, and more. They show some examples of fake images giving a sense of how wide spread this is (or even could be).
In addition, they go into detail talking about Image Analysis through Machine Learning/Artificial Intelligence (ML/AI) using AWS. Though, other cloud platforms such as Microsoft could easily be used for the same purpose with their ML/AI solutions.
First, to get images to look at, Chet took the Python program Tweepy and added a GUI + analytics/filtering to examine and capture tweets in real-time. Unlike other tools, the automatic method may even capture deleted messages more quickly. After that, they pushed it into FIATS (Fake Image Analysis Testing Script) -- an unreleased Python script that he is working on. FIATS uses ML to detect fake/altered images.
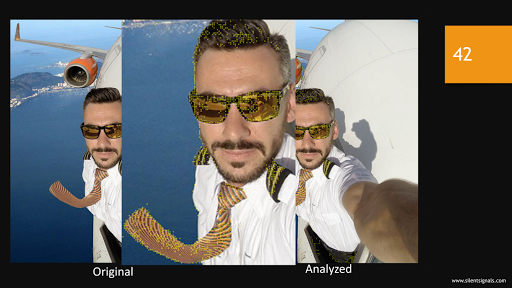
Here, the yellow dots show anomalies where the image mostly likely was edited and spliced together. Another note here, if you look at the reflection in the sunglasses, you can see the picture was taken on the ground based on the look of the shadows.
Preservation & Spoliation of Virtual Meeting & Ephemeral Messages
Speaker: Ronald J. Hedges, Dentons
Virtual meetings have become a stable today as over the past year companies pivoted to find new ways to work as the pandemic raged around the globe. He directly works with the Sedona Conference. The Sedona Conference is a collection of professionals that write publications to understand different areas of law such as Antitrust, Complex Litigation, Data Security & Privacy, eDiscovery, and others. The publications are freely available on their site.
Ronald dives into the what this means on a legal side. What records must be kept and when should they be kept? The same is true for ephemeral messages such as Snapchat. One of the interesting discussions here was the description of a "record" and how long should that information be kept. In some places, governmental and private companies are working to purge old and outdated information to keep legal discovery from locating these kind of records.
One question in the class was about VOIP data streams and if the packets were a record based on some definitions of "record." My professional option is no. First, you would want to capture voice traffic directly from phone exchange (PBX) server or equipment using traditional methods or voice recording software (example: lifesize). Most VOIP solutions currently encrypt traffic by default between phones and the PBX and capturing those packets would provide no usable information and will waste space and will require a solution to capture them. However, recorded conversations should be treated as a "record" when required by laws or local policies.
In Conclusion...
It was a great invent and way too much to watch to. The vendors at the event had plenty of show-in-tell and stuff you can touch and feel ranging from software to hardware to training.
Updates
6/14/2021 22:41: Cost updated for someone to help setup ISO 27001 for you. I was in error that it was $1500 but I was informed by Noel that it was $150,000. It has been corrected.